Root certificate
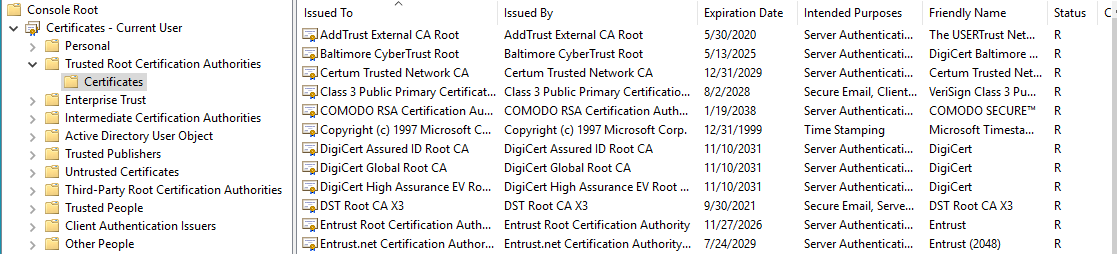
A root certificate identifies a Certificate Authority. With this root certificate a CA signs one or more subordinate certificates, that sign the SSL certificates of end-users. A webbrowsers contains a list with root certificates from trusted CA's. This list may vary per browser, in most cases it has about 600 root certificates on it. As user, you may alter this list manually by deleting or adding root certificates. Below a fragment of the Microsoft Management Console:
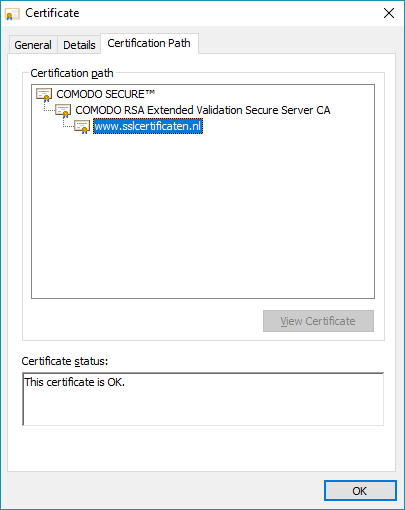
Browsers trust these root certificates. Therefore, the certificates of end-users that are signed by the intermediate certificate (which is directly signed by the root certificate) are automatically trusted. This is what we call a 'chain of trust', or a 'certificate-hierarchy'. The image below shows the hierarchy for the certificate for www.sslcertificaten.nl (You can view the certificate by double clicking on it to open it).
For a correctly functioning SSL certificate, a well supported root certificate is important. Root certificates have a long lifetime of for example 20 years.
Previously, it was common for root certificates to sign end-user certificates directly, without intermediate(s) in between. Nowadays all CA's use one ore more intermediates. Comodo uses a different intermediate for each certificate type. Because the root certificate doesn't need to sign anymore, it doesn't have to be online - this makes it less vulnerable for abuse. After all, if the root certificate becomes compromised, all the subordinate certificates become unusable. That also explains why a CA uses multiple intermediates: if one intermediate becomes compromised, this doesn't effect the other intermediates.
Due to the recent transition from SHA-1 to SHA-2 encryption, nowadays all CA's use SHA-2 intermediate certificates.
SSLCheck
Our SSLCheck will examine your website's root and intermediate certificates for correctness and report any potential issues

