Symantec Reissue
Google and Mozilla have lost faith in Symantec certificates, due to multiple incidents related to their issuing over the past years. Symantec’s SSL division will be taken over by DigiCert, which allows for Symantec certificates to stay trusted in Google Chrome and Mozilla Firefox. Symantec, GeoTrust and Thawte certificates can be exchanged free of charge from December 1, 2017 so that they will continue to be trusted in these browsers.
Planning
Google published its final timeline for terminating support for Symantec certificates in its popular Chrome browser. Mozilla Firefox has also published her planning. As Chrome is the most used browser internationally, we will follow Chrome’s timeline for the reissuance dates.
Impact on certificates in Google Chrome
In order for certificates issued by Symantec, GeoTrust and Thawte to be trusted in major browsers, they need to be exchanged:
- Certificates issued before June 1, 2016, will stop being trusted as of Chrome version 66, due to be released on March 15, 2018. These certificates will need to be exchanged between December 1, 2017 and March 15, 2018
- Certificates issued between June 1, 2016 and December 1, 2017, will stop being trusted as of Chrome version 70. The canary version was released on July 20, 2018, the beta version will be released by September 13, 2018 and the official version by October 16. These certificates will need to be exchanged between December 1, 2017 and October 16, 2018
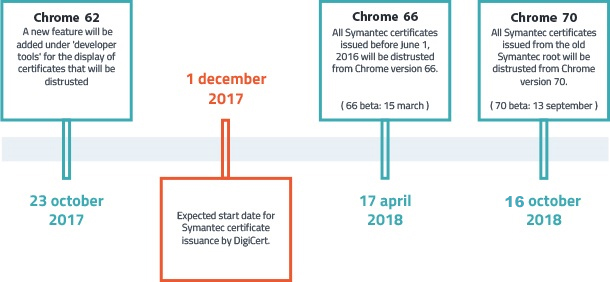
DigiCert issues Symantec certificates from December 1, 2017. Symantec certificates issued by DigiCert will be fully trusted by upcoming Chrome releases.
Impact on certificates in Mozilla Firefox
Early October Mozilla announced to delay the distrust of Symantec certificates. The deadline of Firefox version 63 per October 23, is moved to Firefox 64, which is planned voor December this year. The reason for this is the fact that more than 1 percent of the top million most popular websites still uses the affected Symantec certifcate. This delay gives webites more time to renew their certificates.
The timeline announced by Firefox is as follows:
- As of January 2018 (Firefox version 58), a warning will be shown in the Developer section for Symantec certificates issued before June 1, 2016.
- As of May 2018 (Firefox version 60), a not trusted warning will be shown for Symantec certificates issued before June 1, 2016.
- As of December 2018 (Firefox version 64), all Symantec certificates issued from the former PKI infrastructure (before December 1, 2017) won’t be trusted.
In addition to the browsers, SSLLabs has announced that it will adjust the grading in its SSL Server Test from 1 March 2018 to a T-score, if a website uses a Symantec SSL certificate issued before 1 June 2016.
Exchange procedure
From december 1 2017 you can start to exchange your certificates. You can chose between reissuing them, or depending on the remaining validaty, directly renew them. As an alternative you can switch to another brand. You may switch you certificates to similar Comodo or GlobalSign certificates at no cost of for a reduced price. If you prefer this, please contact us.
Reissue procedure
From December 1, 2017, certificates can be reissued using the following steps.
| Issue date |
Exchange deadline |
| Certificates issued before June 1, 2016 | Exchange before March 15, 2018 |
| Certificates issued after June 1, 2016 | Exchange before October 16, 2018 |
- From early December, certificates due to be exchanged will be shown in the Xolphin Control Panel along with the final reissuing date. Furthermore, information regarding certificates that should be exchanged will be sent via email.
- Choose ‘Reissue’ in the Xolphin Control Panel for every certificate due to be reissued. We recommend generating a new CSR. Alternatively, the previous CSR can be re-used. It can be found in the Control Panel as well.
After a reissue, the old certificate will not be revoked.
With this procedure you'll receive the same certificate type and brand with the same start- and end date, but signed by the new DigiCert rootcertificate.
Note: We notify you in the Control Panel about all certificates issued before December 1, 2017. This may include certificates that expire before the mentioned reissue date. In this case instead of a reissue a regular renewal is sufficient, which is possible from 90 days before the expiration date. Some development environments will start warning sooner - this will not harm most website visitors, but if you want to prevent this you can opt for a free reissue. Certificates that expire before the exchange date, are clearly marked in the Control Panel.
Influence of limitation validity period to 2 years
From March 1 2018, the maximum allowed term for all brands and types of SSL certificates is 825 days (approximately 27 months). If after this date you re-issue a Symantec, Thawte or GeoTrust certificate that is valid for longer than these 825 days at the time of reissue, the remaining term is limited to 825 days. If you do the reissue before 1 March 2018, you will receive a certificate with the original term.
Renewal procedure
With a reissue you'll receive a new certificate with the same start- and end date as the old certificate. To remain trusted in Chrome you might opt for a renewal instead. In this case you'll receive a new certificate with a new validity, plus the remaining validity of the old certificate.
The renewal period for 1-year Symantec, GeoTrust and Thawte certificates is expanded from 40 to 210 days. This allows you to renew earlier, which makes the exchange procedure easier and less time consuming. All Symantec certificates issued before December 1 2017 that have a maximum validity of 210 days can be renewed directly for a maximum period of 1 year. The remaining old validity will be added to the new certificate, rounded up to a full month. For instance: You renew a certificate when it's still valid for 135 days. You'll receive a new certificate with a validity of 1 year and 5 months (the old validity of 135 days/4,5 months rounded up to a full month). Due to the validity limitations set by the CA/B forum, this doesn't apply to 2-year certificates. 2-year certificates still have a 40 day renewal window. To profit from the expanded renewal period, you could renew a 2-year certificate to a 1-year certificate.
Validation
Some certificates require a new round of validation - as such, make sure to request the reissue or renewal in time. Worldwide, millions of certificates will need to be reissued, so take into account a slightly longer delivery time.
- Domain validation certificates require validation via email.
- Organisation and extended validation certificates require a new round of validation of business data, in case the last validation was completed over 27 months ago.
Installation
As soon as the certificate has been reissued, you will receive an email with the new certificates. Aside from the SSL certificate itself, you’ll need to replace the root certificate as well. These can be found in the Download section of the Xolphin Control Panel. Newly issued SSL certificates will be cross-signed by the previous Symantec root to ensure maximum browser compatibility.
Problems between Google and Symantec
In the first quarter of 2017, it became known that Symantec certificates were issued wrongly. After research had been conducted, it became known that Symantec did not monitor its partners, issuing their certificates, sufficiently. These partners issued Symantec certificates in a manner that did not meet the requirements. According to Google, Symantec did not detect shortcomings in a timely manner, and did not respond to reports adequately. Furthermore, Google mentions that Symantec did not make these problems known themselves after finding out.
Google announced they will be terminating support for Symantec, GeoTrust and Thawte certificates in Google Chrome. In August 2017, US-based certificate authority DigiCert announced they will be taking over the entire Symantec PKI division. By implementing DigiCert’s infrastructure, Google’s requirements for safer certificate management are met. As such, Symantec will not need to replace their outdated PKI infrastructure.

Useful information
- Manuals for CSR generation and certificate installation
- Reissue procedure
- Validation procedures
- DigiCert & Symantec FAQ
Related articles
- Delayed delivery of Symantec, GeoTrust and Thawte SSL Certificates
- Google Chrome timeline for Symantec SSL discontinuation
- Google discontinues supporting Symantec certificates, Symantec sells SSL division to DigiCert
- Google and Symantec approaching a resolution
- Google announces measures against Symantec
SSLCheck
Our SSLCheck will examine your website's root and intermediate certificates for correctness and report any potential issues

